Cybersecurity is often mentioned alongside data privacy, and for good reason. With almost everything these days uploaded into cyberspace, the need to secure sensitive information and shield users from the damaging impacts of cyberattacks is fundamental.
While all businesses require cybersecurity, they’re most important in specific government agencies, banking, healthcare, retail, and similar data-sensitive sectors. Enterprises and organizations should hire information technology (IT) professionals to protect important data from being exposed to cyber threats, especially since a study done by the Clark School Of Engineering at the University of Maryland, found that hackers attack every 39 seconds.
The Benefits of Hiring Professionals in Testing Your Cybersecurity System
 You may think that you probably need as much data protection as the next person, and a quick assessment from an IT guy can help you with your cybersecurity needs. The same cannot be said for businesses. This is why businesses rely on expert guides when making critical business decisions. Services like that of Milnsbridge Managed IT can come in handy for businesses needing expert cybersecurity services.
You may think that you probably need as much data protection as the next person, and a quick assessment from an IT guy can help you with your cybersecurity needs. The same cannot be said for businesses. This is why businesses rely on expert guides when making critical business decisions. Services like that of Milnsbridge Managed IT can come in handy for businesses needing expert cybersecurity services.
Taking some steps to prevent data breaches can help your business thrive, and an organization of any size should hire a digital security specialist to protect software and network security systems. The benefits of this include:
Specialized Services
Most general cybersecurity solutions can be done by yourself or your in-house IT team. For instance, you can ask your employees to set up two-factor authentication and avoid using public Wi-Fi when sending business e-mails, among other basic cybersecurity-enhancing activities.
Business-related cybersecurity activities should be established to ensure that your business data is not compromised. There are several components of cybersecurity, which cover both hardware and software assets, that need to be tested in order to ensure business resiliency against cyber threats and cyber-attacks.
Hiring third-party cybersecurity professionals allow an organization to have a clearer understanding of the risks and their vulnerabilities to both perceived and current threats in a specific cybersecurity climate.
Cost-effective
The upfront costs of hiring cybersecurity professionals may be discouraging. But if you consider the value of damages that a weak cybersecurity system can cause, you’ll likely save a lot in the long run. Besides, paying for the monthly salary of an in-house IT specialist is not cheap, either. So are the payments for the regular training that you’ll have to cover to improve the technical skills and knowledge of your IT staff.
Access to Technology
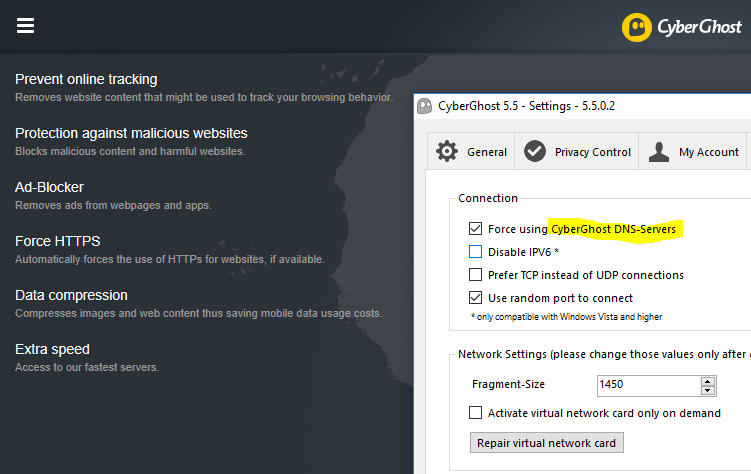
With your in-house IT staff, you’re stuck with cybersecurity solutions that may be obsolete and ineffective in fighting new threats. Cyberhackers are always alert, and proactive, looking for ways in which to penetrate and attack apps, emails, and vulnerable software.
Having cybersecurity professionals test your cybersecurity system allows you to have access to the latest technologies acquired by these firms at high costs. That’s because these experts need to be on top of the innovations in their sector to effectively counter fresh threats.
Peace of Mind
Apart from having the right skills to assess the soundness of a business’s IT structure and to perform the right tests based on your business requirements, cybersecurity professionals are fully aware of emerging threats. In most cases, they can help your business or organization prepare for future vulnerabilities — something that’s quite challenging if you don’t have an in-house IT team that’s equipped with the latest technologies.
Ensures Business Compliance
Authorities are raising the alarm over the scale at which cyber hackers are breaching data protection protocols, and making money out of unsuspecting users. Hence, laws have been crafted to put into question organizations without mitigating measures for data breaches. Newly-passed laws also impose punishment or hefty fines against firms that disregard data protection policies by having weak cybersecurity measures.
Such is the case of the General Data Protection Regulation (GDPR) in the European Union. A similar all-encompassing law has yet to be established in the US, though, but there are existing federal laws intended for specific categories.
Either way, a cybersecurity service provider can help your company meet its obligations to keep your system safe from data breaches.
The Different Components of Cybersecurity
 A cybersecurity system has a few components. Each (or all) of them may be critical to the success of your business operations, so knowing the areas in which you need reinforcement is useful.
A cybersecurity system has a few components. Each (or all) of them may be critical to the success of your business operations, so knowing the areas in which you need reinforcement is useful.
A cybersecurity specialist can be anyone who has the following expertise:
- Application Security: This refers to the steps and activities aimed at making applications more secure. Specifically, these activities may include finding and fixing bugs, as well as enhancing the overall functionality of apps. Application security is generally done by software programmers during the development phase – when they can set up precautions in advance – as well as once the apps are deployed. This is especially important as hackers have become increasingly sophisticated in targeting apps to spread malware.
- Infrastructure Security: Also referred to as data security, activities focus on protecting data from unauthorized access or changes, while it’s being stored and/or transmitted from one machine to another.
Checking for the integrity of your infrastructure includes testing the hardware components such as data hubs, networks, servers, client hardware, and mobile hardware, among other structures.
- Cloud Security: Most businesses currently rely on cloud hosting services, mainly for data storage. Cloud services offer a host of benefits, including accessibility, flexibility, and cost-friendliness. As a cybersecurity component, ‘cloud’ refers to all the technologies, policies, controls, and services that protect all the software and hardware used, and more importantly, all the data is contained in cloud hosting.
- Cryptography: A cryptographer is another IT cybersecurity professional who creates and manages ciphers, algorithms, and security systems, to protect the data from hackers. Encryption methods are used to shield sensitive data from being copied, edited, or deleted. In some cases, a cryptographer can also test systems for any vulnerabilities.
- Vulnerability Assessment and Management: As its name implies, vulnerability management requires searching and analyzing potential weaknesses and flaws in applications and systems. After identification of the issues and problems, they’re addressed based on the magnitude and urgency.
- Incident Response: A reactive manner of cyber protection, this term describes the set of processes and tools used to identify, investigate, and address threats or destructive events. Like real-world emergency responders, cybersecurity incident response entails coming to the rescue of organizations facing system troubles. They should work as fast as possible to mitigate the damages caused by major threats or attacks.
- Disaster recovery: This type of cybersecurity component is somewhat similar to an incident responder, but it’s a more proactive protection response.
In the disaster recovery element of cybersecurity, the IT professional establishes procedures to effectively help organizations prepare for recovery from natural and man-made disasters. Storms, floods, and hurricanes can damage IT infrastructure, weighing heavily on an organization’s recovery effort. Disaster recovery experts aim to mitigate this.
Key Takeaway
Checking the resiliency of your cybersecurity systems requires certain expertise; something that only third-party IT firms can offer. As industry experts, these professionals offer greater efficiency in assessing your business vulnerabilities and laying out strategies to fight off major cyber-threats.