There are a lot of reasons that people choose to use VPNs for their protection while browsing the web. From not wanting your ISP to monitor your web activities all the way to being in a foreign country with more restrictive laws regarding what is allowed versus not allowed in terms of web content, having a VPN is a great way to get out of the miasma of regulatory hell and surf the web without having to bend to the will of a government or a corporation.

As a bonus, using a VPN that does not log your data means your privacy is ensured. That said, many people understand what a VPN is, yet they do not know how a VPN is able to keep data private while allowing unrestricted access to a host of different sites and services.
Why Everyone Should Use a VPN
If you have ever connected to a public network, you have exposed your data to many people, including people who would use that data to do you harm. There are several types of problems associated with public networks, including Wi-Fi spoofing, Firesheep, and Honeypot Attacks, you’re making a significant risk every time you connect to one of these networks – even networks of trusted companies like Starbucks or Target.
Though you may have encrypted connections with your home network, your ISP can still see the different sites and services that you are accessing. If you are torrenting or using streaming services, your ISP will know, and depending on downloading laws; you could be subject to different anti-piracy issues.
Fortunately, VPNs alleviate both concerns.
What Exactly, is a VPN?
 A VPN, or Virtual Private Network, originally was the province of corporate offices. Their intranets were local, on-site networks lacking accessibility from just anyone outside the network. Unless someone knew how to access the network remotely, the corporate intranet was shielded from the world at large.
A VPN, or Virtual Private Network, originally was the province of corporate offices. Their intranets were local, on-site networks lacking accessibility from just anyone outside the network. Unless someone knew how to access the network remotely, the corporate intranet was shielded from the world at large.
Commercial VPN services took it a step further. They created a similar system where users like you could pay for access to their networks. Connecting with a VPN’s servers provide access to the internet that you would otherwise get by using your ISP’s connection. However, when you access a VPN, there are a lot of other things happening that keep your activity private, along with helping your security.
Many VPNs use encryption, and this encryption combined with tunneling is how the VPN can protect your individual network node (e.g., your computer) from problems with a Public Wi-Fi or with your regular home Wi-Fi.
How Does VPN Encryption Work?
Encryption for VPNs is usually either 256-bit encryption or 128 bit. The difference between the two is a level of security and performance. 128-bit encryption allows for faster performance when connecting to the servers, while 256 bit is slower. That said, 256-bit encryption is used by the US Military, and right now, this level of encryption is considered impossible to crack. There is a reason for this – what encryption does is essentially turn the data that you transmit between the server and your computer into gibberish.
Let’s back up a minute. Every time that you open up your browser and type in a website, you are connecting to your ISP’s DNS server. This server then connects to the website. Data transmit back and forth between your computer and the server. With this connection that does not have VPN protection, your ISP sees everything that you do. Every single page you visit, every file you download.
With a VPN, you connect to the VPN server right away – not the DNS server provided by your ISP. Once you start browsing – going to different sites, downloading stuff, using Netflix, for example – your ISP has no idea what you are doing because the data coming from the VPN server is unintelligible numbers and letters that have no meaning.
What you are doing is creating a massive and completely useless set of receipts that no one can figure out. Most ISPs are not interested in monitoring this stuff because it is too costly and time-consuming.
How Does VPN Tunneling Work?
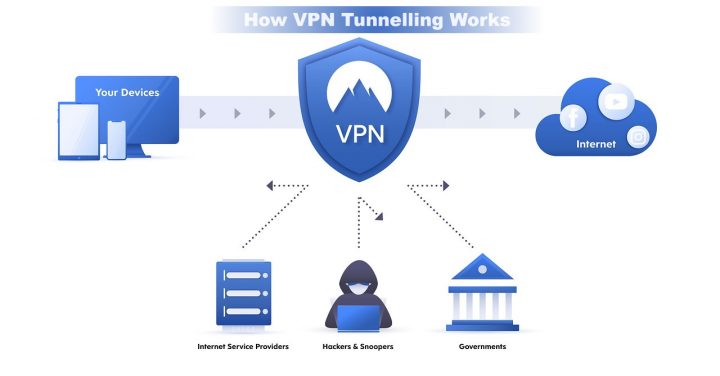
VPN tunneling works with encryption, and it’s mostly a mask that your computer wears when connected to the VPN server. The mask is very important because it conceals your IP address with a generic, randomly generated IP address. Why is this important? Your IP address is how different entities know that you are an individual.
For example, newspapers are able to restrict the number of free articles you read because your IP address is known to them whenever you connect. Using a VPN generates a different IP address, so you can keep changing your IP address and reading free articles despite monthly limits.
For protection, VPN tunneling provides a generic IP address that renders any efforts for hackers to use your IP address to access your network as completely useless. They essentially have a dead-end, and once they realize all of the traffic is encrypted between your IP address and the server, hackers move on to targets that are a lot more easy to access.
So, while you are sipping on a latte and browsing the internet with your VPN, someone else is browsing unprotected, and a hacker is using their IP address to access their information for nefarious purposes.
Finding the Right VPN
The key to finding the right VPN is to get a VPN that has a subscription fee. These VPNs offer military-grade encryption (256 bit) along with many different servers in lots of different countries around the world.
Having a bunch of different servers allows you to connect in different places for masking your activity and if you want to appear like you are in Australian when you are really in a strip mall in White Plains, then having a VPN server with access to sites throughout the country is the best way to do things. Having a VPN is really the best way to protect yourself whenever you are online, browsing from the Airport or other free Wi-Fi.
















This is truly an excellent read. It is one of the most useful piece I’ve read about VPN. It is easily the best way to get out of the miasma of regulatory hell and surf the web without having to bend to the will of a government or a corporation.
Good job, that blog post very informative for me. thanks for share the knowledge about VPN. appreciate your work.