Android as a very popular and arguably the most widely used mobile OS is exposed to more vulnerabilities than other operating systems. Recently, there has been news of newly discovered vulnerabilities that can allow hackers to gain access to Android devices in just a few seconds.
Well, in this article, I’ll list out the top 10 Android vulnerabilities and how to prevent malicious hackers from exploiting these known vulnerabilities.
The 10 Android Vulnerabilities and How to Stop Them
While we can’t easily verify the popularity of these Android vulnerabilities, they were released from trusted security companies who have firsthand knowledge on the severity of these loopholes.
It is good that you know about these popular Android loopholes so as to be careful on how you use/expose your Android devices. CyberAttackers and hackers can easily gain access to compromised devices remotely or without even coming close to them. The problem is growing and the statistics shared by Tiger Mobiles earlier this year show that there are millions of cybercrime victims worldwide, with 17.5 million in the UK last year.
These security tips will help you fix popular Android Vulnerabilities and also prevent hackers from tampering with your Android smartphone and/or tablet devices.
1. BlueBorne
The BlueBorne vulnerability was uncovered by Armis, a security company. According to Armis, this vector is transmitted via Bluetooth and it can allow an attacker to get access to your device without having to touch it. Also, the attack is open to computers as well as IoT devices.
This /vector allows a hacker to find a device, connect to it via Bluetooth, then begin to control the device remotely. It is not as if this is totally secretive because the device will “wake up” while activating the exploits.
How to stay safe against this attack
Always try to update your Android device regularly and keep off from older IoT devices. The issues from BlueBorne vectors should be patched by the top guys in the electronics space, however, unpopular devices may still be vulnerable to this attack.
2. Binary Protection
Not rooting a device properly can expose it to severe attacks. Like you may already know, rooting an Android device bridges the data protection and encryption. Once an Android device gets compromised through root, certainly, any code can run on the device including malicious codes. Hence, it is a bit easier for a hacker to gain access to the device.
Safety tip
Carefully watch out for the apps you install on your Android device especially when it is rooted. Some root apps secretly copy your device data and make them accessible to a third-party (probably a hacker).
3. QuadRoot vulnerability
This is a recent attack on mobile devices powered by Qualcomm’s chipsets. Experienced hackers can possibly gain full access and control over your Android device and personal data using this vulnerability. The latest update from ZoneAlarm shows there are about 4 QuadRoot vulnerabilities:
- CVE-2016-2059
- CVE-2016-2503
- CVE-2016-2504
- CVE-2016-5340
If you have been affected by this vulnerability, the only way to fix your device is to update your OS. Or, if you can contact your device manufacturer or network and ask for a new system update.
4. Stagefright Vulnerability
A lot of vulnerabilities were found on Android Stagefright Media Library. These vulnerabilities will allow a hacker to send crafted Multimedia Messaging Service (MMS) messages to any Android device in order to exploit the vulnerabilities. Sadly, this does not require the user interaction to activate the exploit; the user will be left unnoticed.
The Stagefright vulnerability affects Android devices running on version 2.0 through to the latest version.
How to keep safe from this attack
- Never attempt to open MMS messages from unknown senders: If possible, disable MMS on your Android device until you fully install the required patches from your device manufacturer. Ensure your Android device is updated with the patches from Google to device manufacturers.
- To disable MMS, go to Settings >>> Wireless and Networks >>> Mobile Network, select your current APN and deactivate/remove settings for MMSC, MMS proxy, and MMS port
5. Certifi-Gate Vulnerability
Security research uncovered certificate verification vulnerabilities in Mobile Remote Support Tools (mRSTs) which are often pre-installed on Android devices. These malicious programs may appear legal as they require only but a few permissions, but they exploit the vulnerability to mRSTs in order to connect and access your device.
Certifi-Gate is a tricky vulnerability that allows attackers to gain full control of your Android device, it also exposes your personal data.
An experienced hacker can control your device by exploiting app security certificates to gain rightful access, the main issue is that Android OS doesn’t have enough patches to revoke these certificates.
What to do when your device is already affected
- Uninstall all suspicious apps on your device and ask for OS update from your manufacturer
How to stay safe
- Only install apps from secured app stores
- Constantly update your mobile security software
- When necessary, use secured browsing apps like Surfshark for Android VPN to ensure your browsing sessions are well encrypted and/or protected from prying eyes.
- Add an internet security suite (like Kaspersky internet security), if you think there’s a need for it.
6. HummingBad
This is a virus developed by Yingmob, a Chinese advert company. So far according to reports this virus has affected more than 10 million Android devices. HummingBad is a malware that creates false ad revenue and automatically installs more malicious apps on Android. The HummingBad malware has root access on Android, so, attackers can virtually do anything they like on affected devices.
How to fight against HummingBad
Run a factory reset on your device and reset your Google password from PC so that you’ll now activate your Android with new credentials.
7. Vulnerabilities installed by OEMs

Obviously, hackers could exploit these pre-installed vulnerabilities to carry out a lot of actions on the affected device or even steal their private information by luring a victim to install a malicious app.
The vulnerabilities are different across Android phones, this is because they all have different pre-installed apps. Also, because there are tons of different Android phone makers, Google finds it difficult to keep track of all of the pre-installed apps. However, some manufacturers do a good job by pre-installing only secured apps.
How to stay safe
To prevent theft and data loss from this kind of vulnerability, always read reviews from trusted tech platforms before buying a product from newcomers. Ensure there are some sizeable reviews of their products before opting for the new smartphone manufacturer.
8. SQL Injection
The CVE-2018-14066 vulnerability is associated with SQL injection which is triggered by the content://wappush content provider in com.android.provider.telephony: this is mostly found in some custom ROMs for Android phones.
Research shows that this vulnerability affects Infinix X571 phones, as well as various Lenovo phones that have since been fixed by Lenovo.
9. Man-in-the-Disk attack – MitD
This attack can easily grant 3rd party apps the ability to run malicious codes on an Android device. It was uncovered by the team at CheckPoint as a malware that resolutes around an Android app’s ability to use external storage memory. The Man-in-the-Disk attack is dangerous because it tampers with another app’s External Storage data. Many users fall a victim because most apps request for external storage permission which is somewhat normal.
However, there are security risks attached to granting this permission, you just have to be careful the kind of apps you install. Mostly, this attack is hidden inside malicious flashlight apps.
Pre-installed Google Voice Typing, Google Translate, Yandex Translate, and Yandex Search were vulnerable to crash-type MitD attack, while the popular Xiaomi Browser was vulnerable to the malicious-update-type MitD attack.
Already, Google has rolled out a patch for this vulnerability, so you need to contact your device manufacturer and request for device update to stay safe.
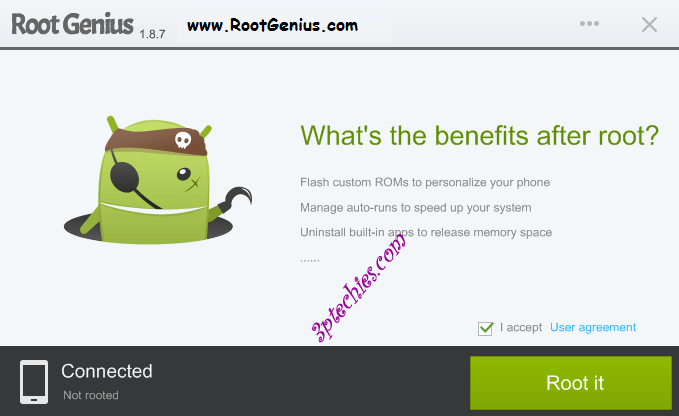
10. Root access vulnerabilities
While rooting an Android device is somewhat good for advanced users, it exposes the device to quite a lot of vulnerabilities. This is because once after rooting a device, the default security patches installed by the manufacturer is voided and if you’re not careful enough, a hacker can easily gain full control over your device.
A lot of malicious exploits work on rooted devices and you cannot request for a patch anymore. This can be very dangerous and will require you to run a factory reset and then root the device again.
Conclusion:
The only way to stop/halt hackers from exploiting these Android vulnerabilities is through patches and running device/OS updates regularly. Google has released several patches to help its users stay off these attacks. On the other hand, rooted devices suffering from any of the vulnerability attacks can be quite difficult to sort; therefore, you may need to flash a new firmware or custom ROM to get rid of the malicious apps that are used by the hackers to exploit your device.
However, the latest Google OS – Android Pie (9.0) is exempted from these vulnerabilities due to the high-security patches it’s saddled with. Know another popular Android vulnerability I didn’t list in this page? Voice them out below.